The upcoming official release of macOS 11, also known as macOS Big Sur, will introduce a change that will make many Mac adware campaigns go down the drain.
Apple is planning to pull the plug on a persistence trick that revolves around installing configuration profiles from the command-line interface. This feature was originally designed as a fundamental functionality of the tech giant’s enterprise package for macOS. It is a shortcut to implementing specific rules and configurations by means of automated scripts at the level of an organization’s IT network. Therefore, system administrators are the primary audience of this feature.
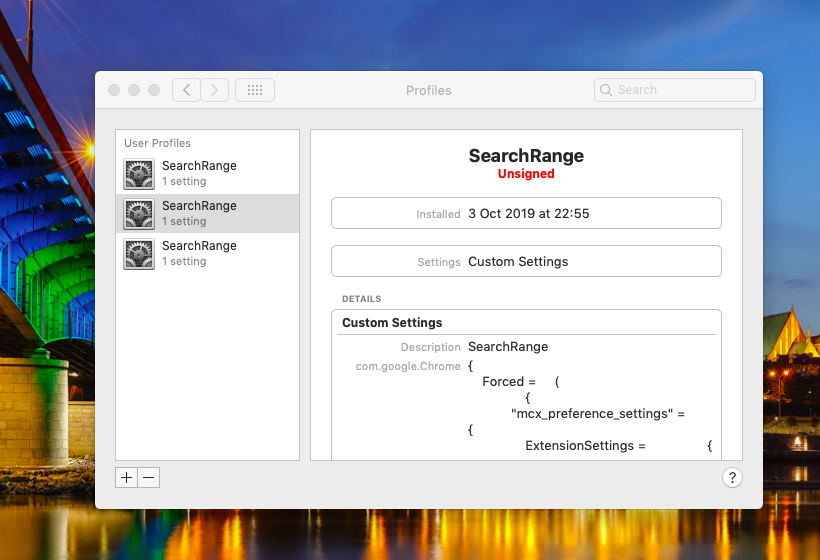
The sad truth is that malicious actors don’t mind mishandling it, to say the least. The ability to manage certain areas of a host system’s behavior via new device profiles is a temptation crooks couldn’t resist. As a result, the vast majority of Mac adware operations carried out over the past several years abused this functionality to specify unwanted web browsing preferences, tweak proxy settings, and modify default applications. This technique is absolutely quiet and doesn’t rely on user interaction at all.
No more interactionless profile installation
This will change with the upcoming macOS Big Sur release onwards. Apple is going to alter the logic of creating configuration profiles. Malicious code will no longer be able to do it via a series of sneaky commands in the Terminal.
Kevin Milden, a member of Apple’s Interface Design team, announced the game-changing move during his talk at the Worldwide Developers Conference 2020. He said that macOS 11 will not allow applications to completely install device profiles using just the Terminal. Instead, when such an attempt is made, the operating system will treat it as a commonplace instance of downloading an app. Therefore, the user will need to additionally green-light the installation manually.
In other words, the process of adding a profile can only be completed as long as the user knowingly agrees to it. Physical access to a Mac is another critical prerequisite for such installation. Obviously, this will cause adware authors to hit an extra roadblock when trying to gain a foothold in infected systems. The workflow won’t be quiet anymore, and therefore crooks will have to add some social engineering to the mix. This, in turn, will dramatically reduce the success rate of such attacks.