Is it possible for a MacBook Air/Pro to get viruses?
Rumors have it that MacBook is a virus-free system. But what exactly a computer virus is? It is a program entering a computer system without proper authorization. Stripped of academic language, we do not want this stuff neither on MacBook nor on any other machine we control, but it sneaks in.
Upon entering a MacBook, true virus propagates by inserting its body into other programs installed. This is its essential trait making the difference from other malicious contents like a trojan or a worm. In practice, common language does not distinguish clearly between types of malicious content. A virus commonly refers to any kind of malware. We follow this approach.
The question thus rather asks whether anything can be added to your MacBook without you knowing that or your permission? Yes, your MacBook, just like any device, can have a virus, as long as it exchanges information with other devices via the Internet, local networks or directly. The simplest situation to imagine is another person gaining access to your device. This person can add viral codes to the software so that it becomes viral or download malicious items from external sources. Such an approach is obviously too laborious so that viruses typically infect your MacBook propagating via the Internet and local networks.

How much MacOS is exposed to viruses
A MacBook Air/Pro, just like any Mac product, is less exposed to any computer threats. In fact, it is not that Apple protects its devices so much better than Microsoft does. It is just that Windows is so much more popular than Mac is. The market for Windows is much bigger. The audience is much bigger. Virus developers thus focus on Windows as it covers the biggest audience.
True, Mac products used to be nearly invulnerable to malware as they initially featured greater protection than Windows, yet due to its smaller share, the market has been less attractive. This was rather underserved security entailing slower progress in Mac anti-virus technologies.
Emerging viruses go hand in hand with evolving antivirus systems. In a way, Windows has got trained to resist viruses. Lots of vendors provide antivirus software for this operating system competing with each other.
Apple operating systems used to represent the opposite situation as hardly any vendors provided antivirus software for the system facing very few emerging viruses. At a certain point, the Mac world realized it was not ready to face a sudden surge of viral activities in its domain.
Recent MacOS malware development
According to the Kaspersky detection report, the number of viral attacks targeting macOS has been growing since 2012. A slight decline is expected in 2019.

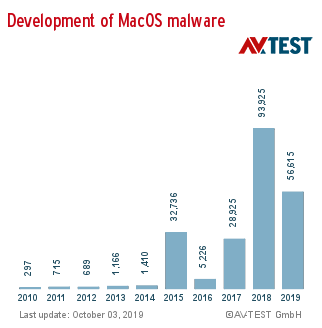
The AV-TEST Institute https://www.av-test.org/en/about-the-institute/ report monitoring macOS malware development since 2010 demonstrates skyrocketing growth during the period of 2016 to 2018.
Both suggest the macOS malware had been very rare to occur before the major surge in 2014 or 2015.
macOS security vs evolving viruses
You might argue that we have failed to mention a critical thing about Mac, its approach to security of its operating system. MacOS uses something called App Sandbox. This keeps any application running on Mac within a kind of container. The Sandbox is a framework establishing the limits to be observed for the app it contains. A Mac application can only access the resources and take actions allocated to it within its Sandbox. Should it try to insert its viral code into other applications or do other damage, the application may get blocked by the Sandbox.

Another Apple technology, Developer ID, restricts access to macOS with the Gatekeeper. The latter is the feature preventing any app from being installed on macOS unless it has an ID assigned by Apple. Leaping up ahead, scams involving Developer ID theft proliferate, as well as there are infections disabling this security feature specifically to implement their payload.
Sandbox actually poses a challenge to the attackers. Statistics suggest that since the technology revamped as App Sandbox back in 2011, macOS had not suffered any major attacks until 2014 or 2015, their number tending to zero. Getting infected was virtually impossible case for a macOS.
Every stick has two ends. Utmost protection provided by advanced and unique technologies implemented in macOS and its somewhat marginal position discouraged hackers for a number of years. This also provided limited incentives and options for Mac security to develop. It overlooked or was not ready to face the major surge in 2014 to 2015. Currently, Mac viruses seem to be in decline, but getting infected is quite possible and much more possible than it was back in 2013.
Can a true virus do damage to macOS?
A narrow definition of a virus excludes trojans and worms. It explicitly refers to a program code propagating itself by adding to other programs. A virus can only execute its payload as long as it functions within its host program.
A number of malware attacks have managed to break through the Gatekeeper. They have provided a stolen or fake Developer ID that Gatekeeper has accepted or exploited a particular vulnerability in that system. The attacks thus dropped their program codes into MacBook overcoming the first level of its defense.
Can we consider any of those attacks to be purely viral? No, we cannot unless we stick to the broad definition that does not distinguish between a virus and a trojan. The attacks observed for a recent decade have not involved any macOS genuine application executing the code they drop. Sandboxing in combination with DeveloperID restricts functionality and resources available to any software installed on macOS (there are few exceptions, but they rather prove the rule). If any app tries to modify its code with the other code it opens, this activity typically gets blocked. Even if not, the software actually affected by a virus can only act within the framework provided by the Sandbox. This discourages attackers from deploying any viral campaigns.
We should not altogether exclude the probability of future virus attacks. DMG files bypassing Gatekeeper verification and involved in software installation might add viral codes to newly-installed apps. Another vulnerability viruses may exploit is the fact that major Mac software often run outside the Sandbox.
Just some five years ago, Mac security was nearly flawless. Currently, the malware your MacBook is exposed to include at least thousands of varieties. Obviously enough, MacBook is no longer virus-free if we imply the broad meaning of a Mac virus. Whether MacBook is ever to face massive attacks of the viruses actually embedded into third-party apps remains to be seen.